One of the primary responsibilities of a GIS application is to maintain data integrity. PHP's validation capabilities are invaluable in ensuring that users submit accurate and complete data. Here are some key considerations:
Client-side vs. Server-side Validation: While client-side validation can provide a smoother user experience, it's crucial to rely on server-side validation as the primary defence. Client-side validation can be bypassed, making server-side validation essential for security.
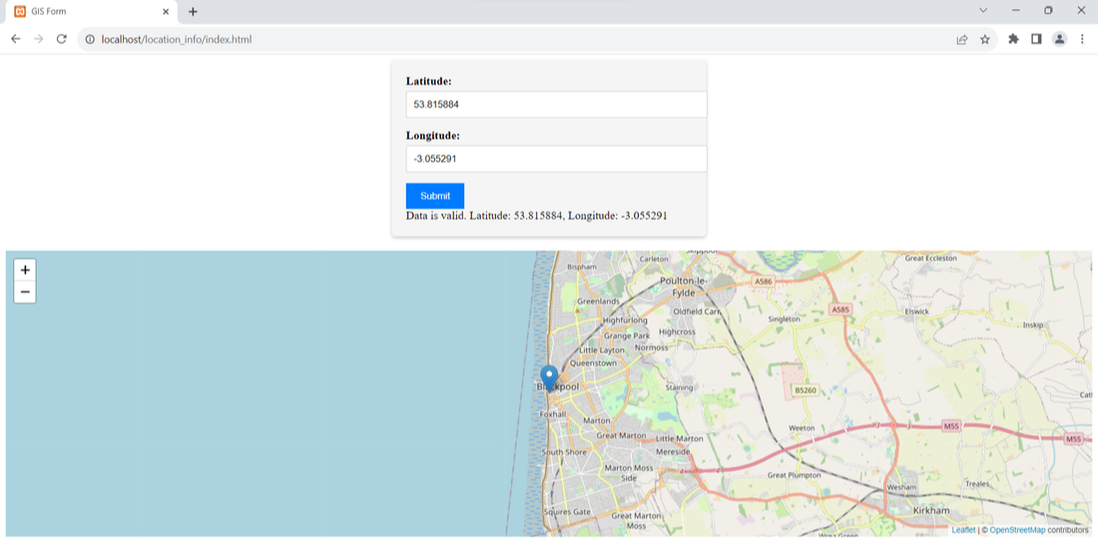
Data Type and Format Validation: Ensure that user input adheres to the expected data types and formats. For example, validate that latitude and longitude values are in the correct numerical format.
Range and Boundary Checks: Implement checks to ensure that input values fall within specified ranges. For instance, you can validate that a user-submitted coordinate lies within the geographic bounds of your map.
Beyond data integrity, security is a paramount concern when dealing with user input. Unsanitised user input can expose your GIS application to various vulnerabilities, including SQL injection and cross-site scripting (XSS) attacks. PHP offers several functions and techniques to mitigate these risks:
Escape User Input: Use functions like mysqli_real_escape_string or prepared statements when interacting with a database. This prevents malicious SQL injection attempts.
HTML Entity Encoding: When displaying user input on web pages, encode it using htmlspecialchars to prevent XSS attacks. This ensures that any potential HTML or JavaScript within the input is treated as plain text.
File Upload Security: If your GIS application allows file uploads, enforce strict controls, such as limiting file types and performing server-side validation to check the uploaded files' integrity.
Regular Expressions: Employ regular expressions to validate and sanitize complex input, such as email addresses or URLs.
Best Practices for GIS Developers
Here are some best practices for GIS developers working with PHP and user input:
2. Error Handling: Implement robust error handling mechanisms to gracefully handle validation errors and provide meaningful feedback to users.
3. Logging: Maintain comprehensive logs of user input, especially when dealing with sensitive data or potentially malicious input. This can assist in troubleshooting and security audits.
4. Regular Updates: Keep your PHP version and libraries up to date to benefit from the latest security patches and enhancements.
Code Example: Enhancing the GIS Form and Map
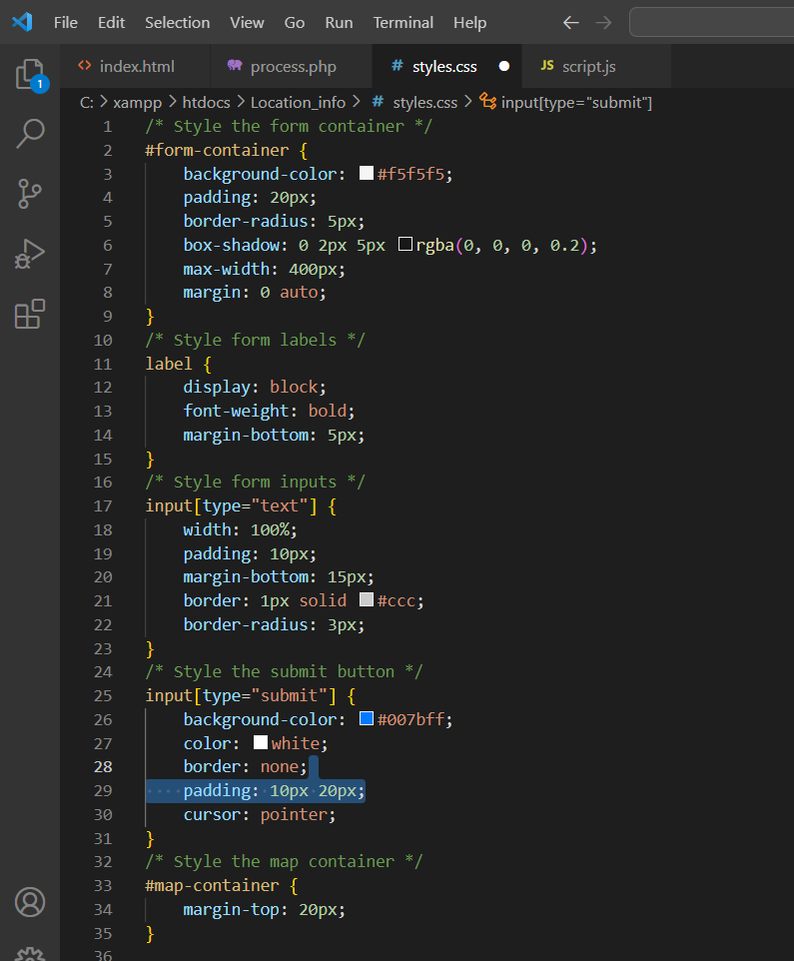
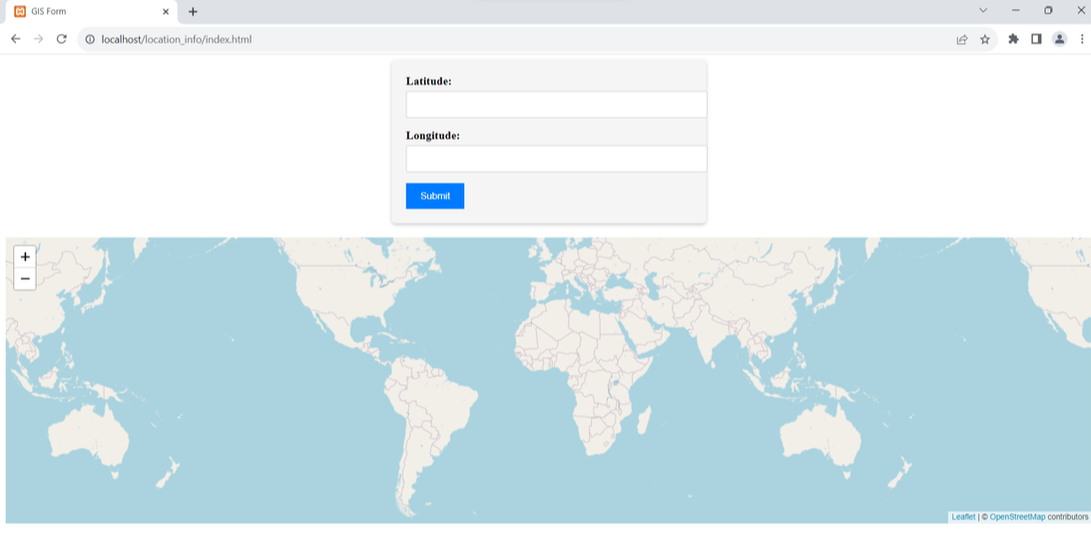
In this section, we'll provide you with a code example that demonstrates how to enhance your GIS form and map with CSS styling.
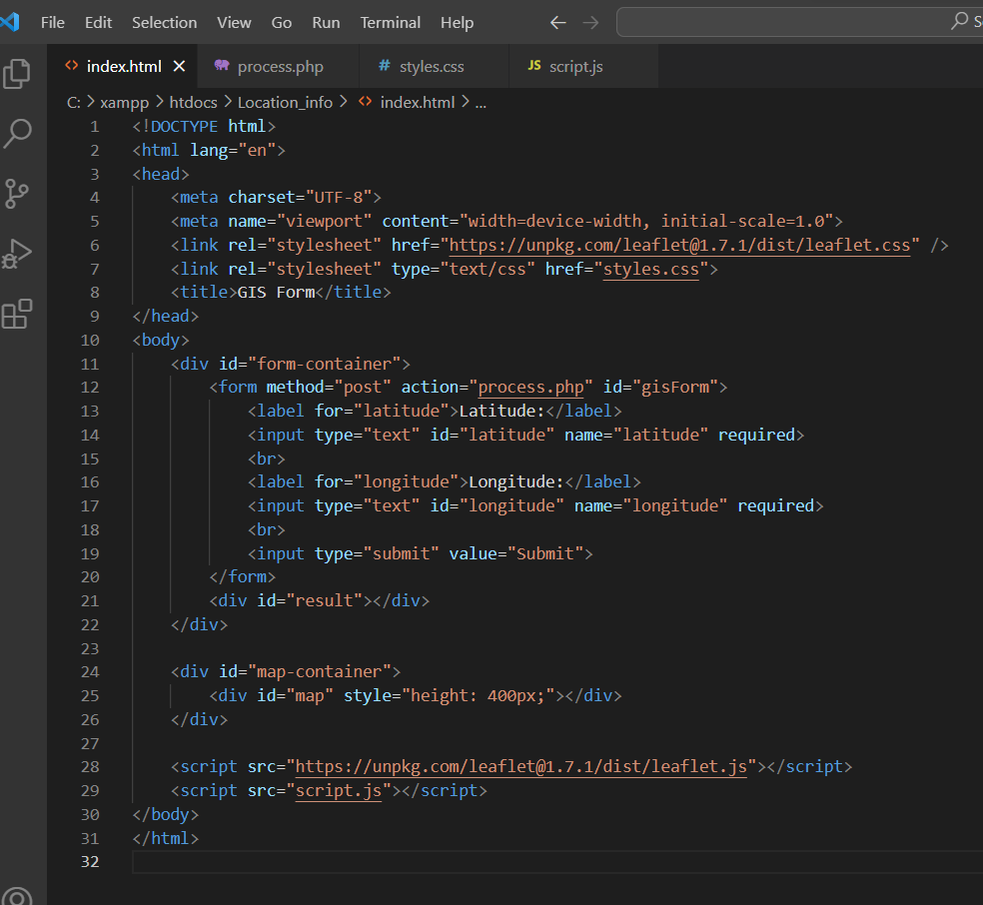
HTML Structure
 RSS Feed
RSS Feed